Pentesting Fundamentals
Task 1 - What is Penetration Testing
Cybersecurity is becoming more important in everyday life, whether it’s creating strong passwords to protect your email or businesses keeping their devices and data safe from harm. You’ve probably seen news stories about hacks or data breaches—this shows how common and serious the issue is.
Even though we’ve gone through what a Penetration Tester here’s recap of what they do.
A penetration test, or pentest, is like a security check. Ethical hackers (pentesters) test the defenses of systems and data to find weaknesses before real attackers do. They use the same tools and methods that hackers might use but with the goal of improving security, not breaking it.
To show how urgent cybersecurity is, Security Magazine reports there are over 2,200 cyberattacks every day—that’s one every 39 seconds!
Task 2 - Penetration Testing Ethics
Cybersecurity often has to deal with tricky questions about what’s legal and what’s ethical, especially when it comes to penetration testing. The words “hacking” and “hacker” often sound bad because movies and news usually show hackers as criminals. But not all hacking is illegal or harmful.
Penetration testing is about legally and ethically testing a system’s defenses. But the idea of someone being allowed to hack into a computer system can be confusing. What makes it okay? The key is an Authorized Audit . Before doing any tests, ethical hackers must get clear approval from the company or organization that owns the system. This permission is like a signed agreement that says, “You can test our system to help us find and fix weaknesses.” Without that approval, it would be illegal.
So, the difference between illegal hacking and ethical hacking is about intent and permission: one harms without consent, while the other helps with consent.
Companies that offer penetration testing must follow strict rules and meet industry standards to ensure they are operating legally and responsibly. In the UK, for example, the National Cyber Security Centre (NCSC) has a program called CHECK. Only companies approved by CHECK are allowed to perform penetration tests on government systems and critical infrastructure. This ensures the tests are done by trusted professionals.
When it comes to ethics, it’s about deciding what is right or wrong. Something might be legal, but it could still feel morally wrong to some people. Penetration testers often face these ethical dilemmas. For example, during a test, they might access sensitive information in a database or trick an employee into clicking on a phishing email to test the company’s defenses. If the company agreed to these actions beforehand, they are legal, but some people might still question whether they are ethically right.
Types of Ethical hackers
White Hat Hackers:
White hat hackers are the “good guys” of the hacking world. They work within the law and use their skills to help others, usually by improving security. For example, if a company hires someone to test its security by trying to find weaknesses in its systems (with permission), that person is a white hat hacker. They’re doing it to help the company fix problems and stay safe from real threats.
Grey Hat Hackers:
Grey Hat These people use their skills to benefit others often; however, they do not respect/follow the law or ethical standards at all times. For example, someone taking down a scamming site.
Black Hat Hackers:
These people are criminals and often seek to damage organisations or gain some form of financial benefit at the cost of others. For example, ransomware authors infect devices with malicious code and hold data for ransom.
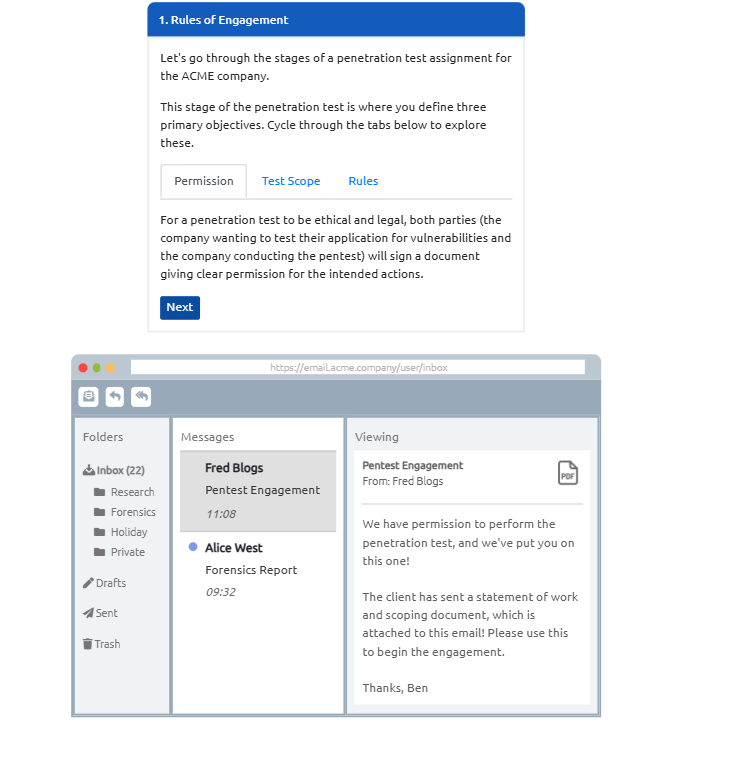
Rules of engagement (ROE)
The Rules of Engagement (ROE) is a document created at the start of a penetration test. It acts like a game plan, laying out clear rules about how the test will be done. This document has three main sections (described in the table below) that guide how the testing will take place, what is allowed, and what isn’t. It ensures everyone—the testers and the company—are on the same page to avoid misunderstandings or unexpected issues.
The SANS Institute provides a great example of what this document looks like, and you can check it out here.
Permission: This is like getting a signed agreement that says, “Yes, you are allowed to do this work.” It’s important because it ensures that everyone involved is legally protected when performing the activities.
Test Scope: This tells you exactly what you can and cannot test. For example, it might say, “You can test these three servers, but you can’t touch anything else.” It’s like being told which rooms in a house you’re allowed to enter.
Rules: These are the do’s and don’ts of the work. For instance, it might say, “You can use some tricks to test security, but don’t trick employees with fake emails (phishing).” It makes sure the work is done in an ethical and agreed.
Question
You are given permission to perform a security audit on an organisation; what type of hacker would you be?
Click to see Answer
White HatQuestion
You attack an organisation and steal their data, what type of hacker would you be?
Click to see Answer
Black HatQuestion
What document defines how a penetration testing engagement should be carried out?
Click to see Answer
Rules of EngagementTask 3 Penetration Testing Methodologies
Penetration testing is like problem-solving: the goal and what you’re testing can vary a lot. Because of this, there’s no single way to do it that works for every situation.
The methodology is the step-by-step plan the tester follows during the job. A good methodology is flexible and fits the specific task. For example, the steps you’d follow to check the security of a website would be very different from those you’d use to test a whole network. It’s about using the right approach for the job.
This is the usual order of a pentest:
Information Gathering:
This is like doing detective work. You gather all the publicly available information about the target, such as details from websites, social media, or other public sources. At this stage, you’re just researching—not touching or scanning any systems.
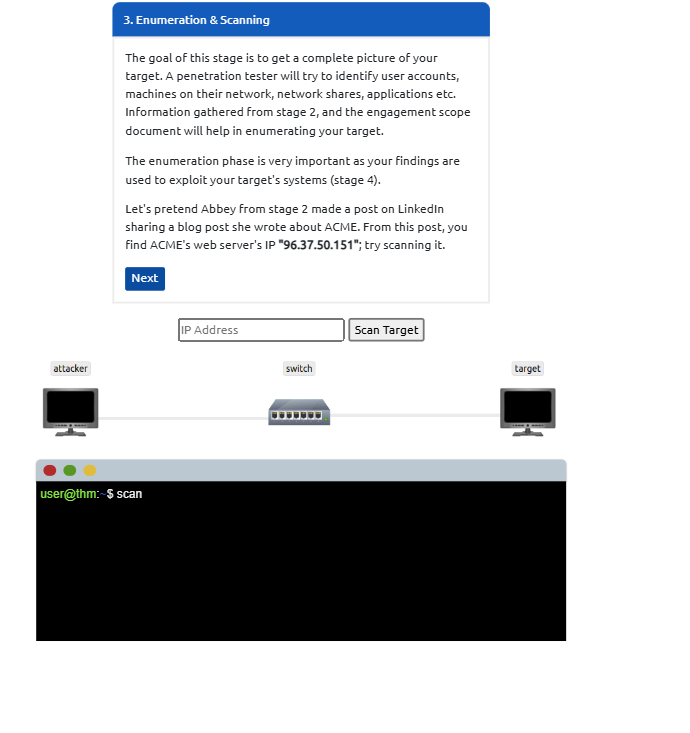
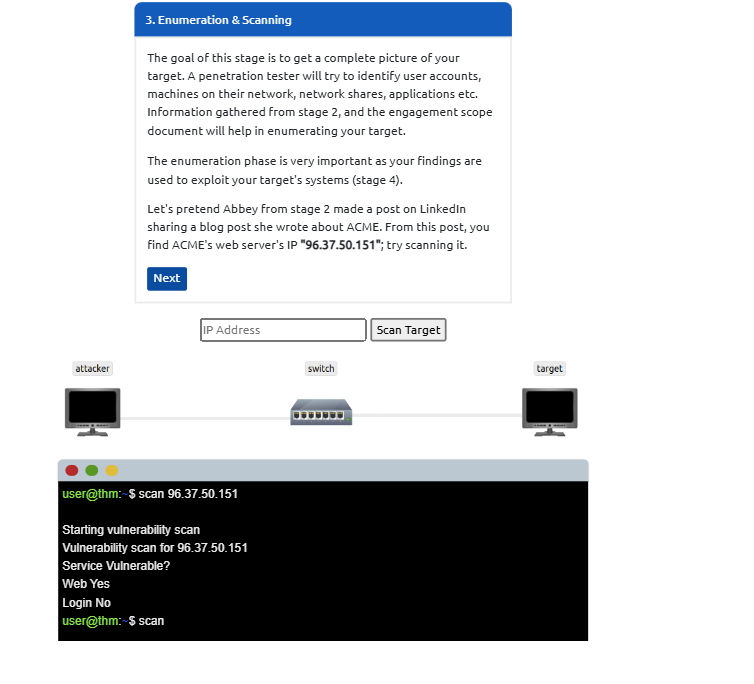
Enumeration/Scanning:
Now, you check what’s running on the target systems. It’s like figuring out which doors and windows are open in a house. For example, you might find a website or other services that could have weaknesses.
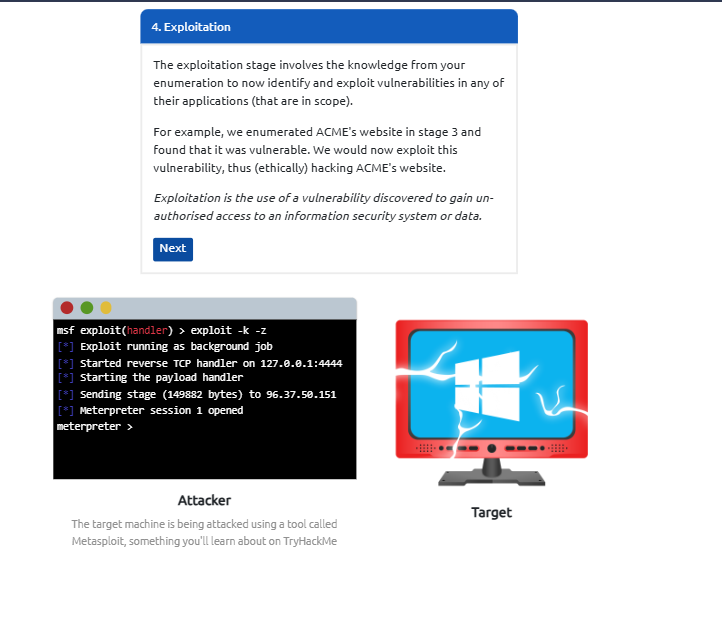
Exploitation:
This is where you test the weaknesses you found to see if you can break in. For example, you might use tools or tricks to exploit a security hole in an application.
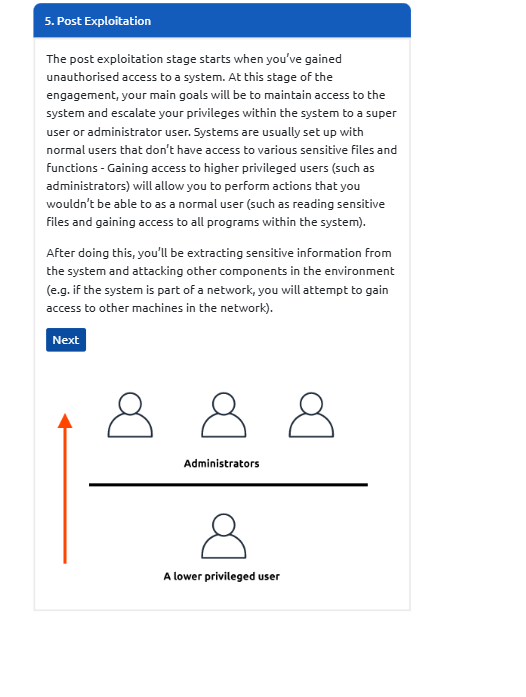
Privilege Escalation:
After getting in, you try to increase your access.
HorizontalEscalation: Accessing another user’s account at the same level.
Vertical Escalation
Gaining higher-level permissions, like an administrator’s account.
Post-Exploitation:
After gaining control, you:
Look for other systems to attack (pivoting).
Gather more sensitive information now that you have more access.
Cover your tracks so your activity isn’t detected.
Prepare a report to explain what you found and how you did it.
Known Penetration Testing Methodologies in the Cybersecurity:
 The Open Source Security Testing Methodology Manual (OSSTMM) is like a detailed guidebook for testing the security of different parts of technology. It helps pentesters figure out the best ways to check for weaknesses.
The Open Source Security Testing Methodology Manual (OSSTMM) is like a detailed guidebook for testing the security of different parts of technology. It helps pentesters figure out the best ways to check for weaknesses.
It focuses on how systems and applications communicate with each other, so it provides specific methods to test things like:
Telecommunications: Phones, internet calling (VoIP), and similar systems.
s
Wired Networks: Systems connected with cables, like office networks.
Wireless Communications: Things like Wi-Fi or Bluetooth connections.
It’s about understanding how these systems work and ensuring they’re secure.
 The Open Web Application Security Project (OWASP) is like a helpful guide for people who create or manage websites and online services. It’s a global community of experts who focus on keeping web applications safe from hackers and other security problems.
The Open Web Application Security Project (OWASP) is like a helpful guide for people who create or manage websites and online services. It’s a global community of experts who focus on keeping web applications safe from hackers and other security problems.
One of the most well-known things OWASP does is put together a “Top 10” list of the most common security issues that websites might have. Think of it like a list of common problems, such as leaving your house doors unlocked or using a weak password. This list not only points out the problems but also explains:
What the problem is – For example, how hackers might steal information or take control of the site. How to check for it – Like a step-by-step guide for spotting these issues. How to fix it – Practical advice to secure the site and prevent future problems. The OWASP framework is updated regularly, so it’s like a living manual that stays up to date with the latest tricks hackers might use. It’s not just for tech experts—it’s meant to help anyone who wants to make their website or online service safer for users.
 The NIST Cybersecurity Framework 1.1 is a set of guidelines created to help organizations protect their systems and data from cyber threats. It provides a roadmap for improving an organization’s cybersecurity by outlining key actions to take in five core areas:
The NIST Cybersecurity Framework 1.1 is a set of guidelines created to help organizations protect their systems and data from cyber threats. It provides a roadmap for improving an organization’s cybersecurity by outlining key actions to take in five core areas:
Identify: Understand the risks your organization faces, including what assets need protection (like data or hardware), and how vulnerable they are.
Protect: Put in place measures to safeguard systems and data from attacks, such as firewalls, encryption, or employee training.
Detect: Set up systems to detect any security breaches or unusual activity, like monitoring software that alerts when something goes wrong.
Respond: When a security breach happens, have a plan to contain the damage and get things back to normal quickly.
Recover: After an attack, work on restoring systems and processes, and improve defences to prevent future attacks.
The NIST Framework also mentions the role of penetration testing (pen testing), While the framework doesn’t go into extreme detail about how a penetration tester should work, it suggests that pen testers can help identify weaknesses in the “Identify” and “Detect” stages of the framework. Essentially, they simulate real-world cyber-attacks to find vulnerabilities before attackers can exploit them as mentioned before.
 The Cyber Assessment Framework (CAF) is a set of guidelines that help organizations, especially those providing essential services like hospitals, banks, or utilities, protect themselves from cyber threats. It looks at 14 key areas to assess how well an organization is defending itself against cyber risks.
The Cyber Assessment Framework (CAF) is a set of guidelines that help organizations, especially those providing essential services like hospitals, banks, or utilities, protect themselves from cyber threats. It looks at 14 key areas to assess how well an organization is defending itself against cyber risks.
Here’s a simple breakdown of the main areas it focuses on:
Data Security: How well is sensitive information (like personal data or financial records) protected from unauthorized access or theft?
System Security: How secure are the computer systems and software the organization uses to prevent hacking or damage?
Identity and Access Control: Who can access certain systems or data, and how is that access controlled to ensure only the right people can get in?
Resiliency: How well can the organization keep functioning if a cyber attack happens, ensuring they can still provide services even during disruptions?
Monitoring: How well does the organization watch for unusual activities or potential threats so they can react quickly?
Response and Recovery Planning: If a cyber attack does occur, how prepared is the organization to respond and recover quickly to minimize damage?
In short, the CAF helps organizations figure out how well they’re protecting themselves from cyber risks and what areas they need to improve to stay safe.
Question
What stage of penetration testing involves using publicly available information
Click to see Answer
Information GatheringQuestion
If you wanted to use a framework for pentesting telecommunications, what framework would you use? Note: We’re looking for the acronym here and not the full name.
Click to see Answer
OSSTMMQuestion
What framework focuses on the testing of web applications?
Click to see Answer
OWASPTask 4 - Black box, White box, Grey box Penetration Testing
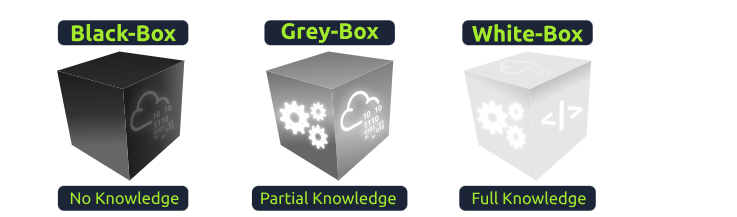
Black-Box Testing
Imagine you’re using an app or website without knowing anything about how it works inside. You only see the things you can click, type, or interact with. Your job is to check if everything works as expected — like clicking a button and seeing the right result. You don’t need to understand the code or the details behind how things function. You’re just testing from the user’s perspective.
Grey-Box Testing
Now, think of this as a mix between Black-Box and White-Box testing. In Grey-Box testing, you know a little about how the system works, but you’re still mostly testing from the user’s perspective. For example, you might have some knowledge of how the app is built, but you still don’t see all the details. This can help you find problems more quickly because you have some background knowledge, but you’re still testing like an outsider.
White-Box Testing
This is the most in-depth type of testing. Imagine you’re a developer who knows all about the app’s code, how it works inside, and what everything is supposed to do. You test the internal parts of the system to make sure everything runs smoothly. You can see everything — the inner workings of the app — and can test it thoroughly. This type of testing is detailed and takes more time because you’re checking everything in the system to make sure it’s perfect.
In short:
Black-Box: Test from the outside with no inside knowledge.
Grey-Box: Test from the outside with some inside knowledge.
White-Box: Test from the inside with full knowledge of how everything works.
Question
You are asked to test an application but are not given access to its source code - what testing process is this?
Click to see Answer
Black BoxQuestion
You are asked to test a website, and you are given access to the source code - what testing process is this?
Click to see Answer
White BoxTask 5 - Practical: ACME Penetration Test
ACME has approached you for an assignment. They want you to carry out the stages of a penetration test on their infrastructure. View the site (by clicking the green button on this task) and follow the guided instructions to complete this exercise.
Question
Complete the penetration test engagement against ACME’s infrastructure.


The main goal here was to understand the birds eye view of the whole proecss of hacking. In this case it was a website. It’s not always a website. But the methodology is usually similar